What is Token Authentication and How Does It Work?
Many of you mentioned that video piracy is a top concern for you today, and you wanted to know what digital solutions are available to curb this. In a previous infographic, we have discussed the state of the video streaming market and piracy in 2019, and have presented some tips on how to fight pirates. In today’s post, we are going to explore one of the solutions we discussed in the infographic and that you highly requested, which is ”How token-based authentication can help you to restrict access to your video content to only authorized users”. We will also examine why token authentication is becoming so popular lately for securing web apps in general!
Token-based authentication is a modern method for user authentication on web applications and websites.
To understand how it works, let us first go through what exactly happens during user authentication. Then we will cover how token-based authentication works and what the benefits of using this approach are!
Today web applications have become increasingly sophisticated, and many of them require users to create an account to access specific services within the application.
Upon creating the account, the user is given account credentials. With the account credentials, the user can log in, and then access specific and relevant information & services on the web application. The account credentials usually consist of a login ID and a password.
However, this password-based authentication suffers from a few drawbacks. Because passwords are user-generated, they can be circumvented or phished by hackers, which could potentially lead to data-breach and data-loss.
To address this challenge, other authentication systems such as biometrics have become popular, as they are unique and irreplicable, depending on the user’s biological makeup, retina, or fingerprints.
However, biometric-authentication is considered less reliable than digital authentication. Also, biometric systems often carry a digital back-up, which make them susceptible to attack two on fronts.
To address these shortcomings, token-based authentication has recently become popular among companies. Token-based authentication has certain features that make it reliable. We will cover them in the next section.
Three essential parameters are used to evaluate the usefulness of any particular authentication method:
1-Usability: How natural and hassle-free does the end-user find it?
2-Security: How difficult is it for a malicious actor to trick?
3-Deployability: How easy is it to deploy the authentication systems for all users across platforms?
Now, let’s discuss how the token-based authentication differs from the password-based authentication.
How Does Token-Based Authentication Differ?
User authentication is an essential first step for many websites and web applications, especially those that provide restricted data access to registered/ qualified users only.
A standard way of authenticating is via the use of passwords that are linked to the User ID. However, the traditional way of using passwords to allow access runs into specific problems.
Mainly because they can get leaked or misused. Most passwords are user-generated and can be hacked or phished.
Password-based authentication can be seen as inconvenient and as a security risk, even if it is done over HTTP.
Also, with passwords, authentication needs to be done for each additional protected resource.
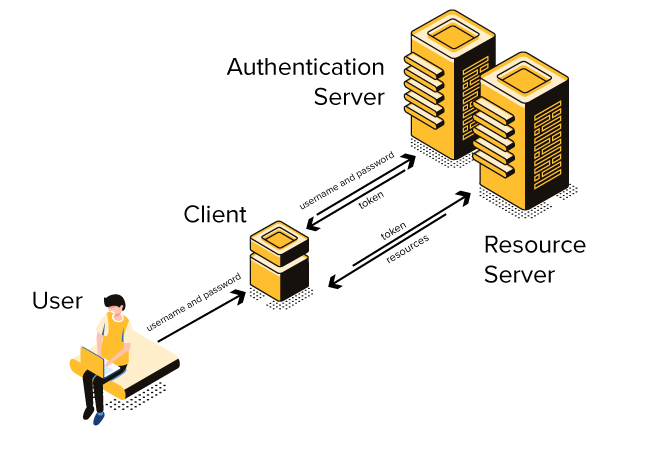
What token authentication does here, is add a level of indirect authentication.
When the user session starts by logging into an app, he/she receives a token from the server. The token has an expiry time, after which it cannot be used.
A token is essentially a machine-generated (generally random) sequence of characters that can be used to authenticate an entire user-session.
Now, the client application can use the authentication credentials to create the authentication token, and in subsequent requests, the app will only send the token.
When the server receives the token, it looks up the credentials of the user to determine if the user is authorized to view the information that it has requested.
When the user logs out of the application, the token gets terminated.
After the token expires, a new token needs to be obtained for continuing with the application. This way, it mitigates the security risk if the token gets leaked. Additionally, token-based authentication consists of a security algorithm that can block it in case the token has been tampered with.
Why is Token-Based Authentication Becoming Popular Today?
The token is stateless, and hence it helps reduce the load on the server. All the information can be stored within the token meta-data itself, and the server and client can exchange the token back and forth, without the need to store the user or session data.
Token-based authentication becomes especially handy in the case of services that require the user to do multiple logins or switch to different application systems during the user session. The user might not be willing to trust multiple applications with their username/ password.
The user need not do multiple logins, but instead can pass the token that they have been given to the other application system, which they’re willing to trust for a limited time.
This also happens, for example, when the web app needs to redirect the user to another server or domain (an example is an e-commerce system redirecting the user to a payment site).
Typically, in this case, the user should be required to login once again. But with token-based authentication, the server can authenticate the user without the need to ask for a new login. This leads to an improved user experience by saving the user time & effort. Multi-logins also make it more vulnerable to password attacks.
When multiple servers are used to host an application, the user information can be sent within the token meta-data itself, reducing the load on the server to validate the credentials.
In short, tokens help to secure your application and improve your website.
Token-based authentication also helps protect the application against CSRF (Cross-Site Request Forgery).
Thus, token-based authentication is more secure, mobile-ready, and easily scalable without putting undue strain on your servers.
Tokens are crucial in helping you secure your applications and help deliver a positive user experience within your web application. With token authentication, you can ensure that the video content on your web application can only be accessed by the authorized user – curbing content piracy.
At Medianova, we provide global CDN solutions in streaming, encoding, caching, micro caching, hybrid CDN, and website acceleration. We have delivered and managed CDNs for leading enterprises, and our state-of-art solutions are benchmarked against industry-leading quality parameters.